Details have emerged about a high severity security vulnerability affecting a software driver used in HP, Xerox, and Samsung printers that has remained undetected since 2005.
Tracked as CVE-2021-3438 (CVSS score: 8.8), the issue concerns a buffer overflow in a print driver installer package named “SSPORT.SYS” that can enable remote privilege and arbitrary code execution. Hundreds of millions of printers have been released worldwide to date with the vulnerable driver in question.
However, there is no evidence that the flaw was abused in real-world attacks.
“A potential buffer overflow in the software drivers for certain HP LaserJet products and Samsung product printers could lead to an escalation of privilege,” according to an advisory published in May.
The issue was reported to HP by threat intelligence researchers from SentinelLabs on February 18, 2021, following which remedies have been published for the affected printers as of May 19, 2021.
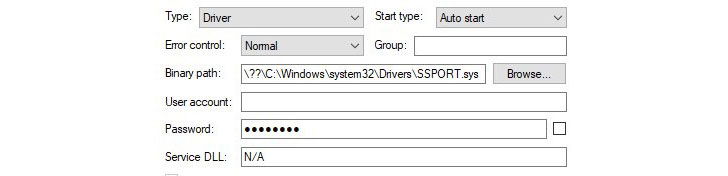
Specifically, the issue hinges on the fact that the printer driver doesn’t sanitize the size of the user input, potentially allowing an unprivileged user to escalate privileges and run malicious code in kernel mode on systems that have the buggy driver installed. now
“The vulnerable function inside the driver accepts data sent from User Mode via IOCTL (Input/Output Control) without validating the size parameter,” SentinelOne researcher Asaf Amir said in a report shared with The Hacker News. “This function copies a string from the user input using ‘strncpy‘ with a size parameter that is controlled by the user. Essentially, this allows attackers to overrun the buffer used by the driver.”
Interestingly, it appears that HP copied the driver’s functionality from a near-identical Windows driver sample published by Microsoft, although the sample project in itself doesn’t contain the vulnerability.
This is not the first time security flaws have been discovered in old software drivers. Earlier this May, SentinelOne revealed details about multiple critical privilege escalation vulnerabilities in Dell’s firmware update driver named “dbutil_2_3.sys” that went undisclosed for more than 12 years.
Credit: The Hackers News

